Banner Image by Pixabay from Pexels
It’s no secret that the attack surface is expanding – and quite
rapidly. Factors such as IT/OT convergence, digitalization, and the
relative immaturity of the Oil & Gas industry in terms of their security
posture all contribute towards the plethora of cyber-attacks this industry is
facing. In the past, these environments were air-gapped, meaning that the only
way to access them was to physically hop over a fence and access the internal
network. This is no longer the case, and organisations around the world are
starting to notice the impact this has on their operations.
This article covers high-profile hacks, case-studies, the
potential impact of being compromised, and how you can mitigate this risk using
Operational Technology Security Solutions.
Hardware and software that detects or causes a change, through the direct monitoring and/or control of industrial equipment. (Gartner, 2023)
The network of physical objects that contain embedded technology to communicate and sense or interact with their internal states or the external environment. (Gartner, 2023)
The integration of Information Technology (IT) systems with Operational Technology (OT) systems. (TechTarget, 2023)
The use of digital technologies to change a business model and provide new revenue and value-producing opportunities. (Gartner, 2023)
A security measure that involves isolating a computer or network from external environments. (TechTarget, 2023)
An information system used to control industrial processes such as manufacturing, product handling, and distribution. (NIST, 2023)
A specialty purpose computer, including input/output processing and serial communications, used for executing control programs, especially control logic and complex interlock sequences. (Gartner, 2023)
Technology that supports threat detection, compliance and security incident management through the collection and analysis of security events. (Gartner, 2023)
An in-house or outsourced team security professionals that monitor and organization’s entire IT infrastructure to detect and address cyber security events. (IBM, 2023)
The Colonial Pipeline Hack

In May 2021, Colonial Pipelines – America’s largest refined oil pipeline, fell victim to a ransomware attack. Transporting more than 100 million gallons of fuel daily, this hack led to consumers, airlines & industries along the entire East Coast being affected. The hack was declared as a national security threat and led to a state of emergency being declared by the country’s president.
Spanning almost 9000 kilometres, (5500 miles) this pipeline is integral to moving oil from the Gulf of Mexico to the East Coast and its states. It supplies about half of the fuel that the East Coast uses, consisting of refined oil, petrol, jet fuel, and home heating oil. As it stands, the Colonial Pipeline hack is the largest publicly disclosed cyber-attack against critical infrastructure in the United States.
The hacker group DarkSide, initially gained access to the Colonial Pipeline network via a compromised VPN password. This allowed them to steal more than 100 gigabytes of data within a mere two-hour period. From there, the malicious actors infected their IT infrastructure with ransomware that affected everything from their computer systems to their financial software.
But what does this hack have to do with OT & IoT security? Between May 7, 2021 and May 12, 2021 – the entirety of the pipeline was out of commission. This means that your average consumer was unable to get fuel, businesses couldn’t refuel their vehicles and factories couldn’t manufacture their goods. IT/OT Convergence is the reason for this. Although there is a myriad of benefits to integrating your systems, they come at the risk of exposing your entire business to malicious actors.
On May 7, 2021 – Colonial Pipelines had no choice but to take their pipeline offline to reduce the risk of exposing the ransomware to their operational network. If malicious actors gain access to OT infrastructure, the impact could be catastrophic – even fatal. Data loss and ransoms being paid are a luxury when the risk of terrorism against critical infrastructure such as fuel lines are present.
Case Study: Operational Benefit of OT & IoT Visibility
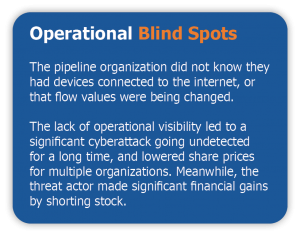 In order to understand the issues with securing Oil & Gas operations, let’s look at a real-world example that recently occurred. A multi-use pipeline transporting both oil and gas throughout North America was experiencing issues allocating volume production between each refinery.
In order to understand the issues with securing Oil & Gas operations, let’s look at a real-world example that recently occurred. A multi-use pipeline transporting both oil and gas throughout North America was experiencing issues allocating volume production between each refinery.
“Whatever you’re reporting was not what we metered, and we are not going to pay for that,” refinery employees would tell producers. The differences had to be disclosed since the companies in question were publicly traded, and the news negatively affected their stock values.
The investigation was started because of the allocation issues. Before built-in visibility, employees would calibrate their meters and transmitters to perform volume research. They would examine the flow computers’ code and examine the flow of data from the flow computers to the control system. Subsequently, they would examine the product marketing system, accounting software, and data historian. Troubleshooting was a tedious, time-consuming procedure. Despite the fact that each allocation problem was seemingly minor at first, a thorough analysis revealed that over time they compounded up and significantly affected the volume of production. Moreover, intriguing and non-random patterns were discovered.
 Industrial control systems (ICS), like the ones that run the pipelines of today, are extremely diversified in their equipment mix and span great distances. Operators had an impossible burden up until recently: controlling and keeping an eye on a system that was difficult to visualize and had inadequate documentation. These devices also generate mountains of data. An operator doesn’t really sure what to focus on because there is too much data. Furthermore, a problem can be undiscovered if no one is examining it from an analytics or security standpoint. After all, production throughput, downtime, and safety concerns are the pipeline managers’ main concerns—not security.
Industrial control systems (ICS), like the ones that run the pipelines of today, are extremely diversified in their equipment mix and span great distances. Operators had an impossible burden up until recently: controlling and keeping an eye on a system that was difficult to visualize and had inadequate documentation. These devices also generate mountains of data. An operator doesn’t really sure what to focus on because there is too much data. Furthermore, a problem can be undiscovered if no one is examining it from an analytics or security standpoint. After all, production throughput, downtime, and safety concerns are the pipeline managers’ main concerns—not security.The Impact of Being Compromised
A Ponemon Institute study indicates that during the previous 12 months, 68 percent of operational technology (OT) organizations experienced a security breach that resulted in the loss of private data or an interruption to business as usual. Furthermore, respondents believe that, on average, 46% of cyber-attacks go unnoticed. A Polaris Market Research report also found that the midstream oil and gas equipment market would grow by $286.56 billion by 2026.
Mitigating Risk & The Solution
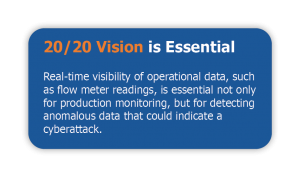
Although essential, traditional security measures are no longer the solution to securing infrastructure in the Oil & Gas industry. But, OT & IoT technology is paving the way to a comprehensive and cost-effective solution. IoT sensors, as depicted above can be rolled out throughout pipelines that monitor for essential functions such as flow rate, pressure, and volume. From here, anomalies can be identified and remediated. Not only does this provide an early-detection system for cyber-attacks, but it also allows providers to identify potential operational failures such as leaks.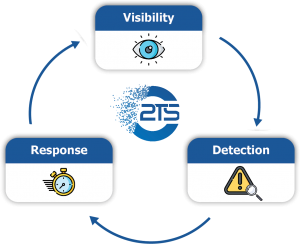
This real-time monitoring can provide insightful data to enhance existing security protocols. For example, if there is significant theft around a specific time frame, physical security can be bolstered at these hotspots. In general, implementing a robust OT security solution can lead to operational cost savings, enhanced security, better decision making, as well as environmental benefits.
Designed to protect mission-critical environments across all operational industries, particularly Oil & Gas, Nozomi Network’s industrial cyber security solution is unmatched in visibility, detection, and response. It integrates seamlessly with SIEM and SOC systems and has the flexibility to be customized to each solution.
2TS is a proud MSSP Focus Partner for Nozomi Networks in Africa and beyond. We boast the highest number of Nozomi Networks Certified Engineers in Africa and manage sites using their technology on a global scale.










Industrial sectors such as Oil & Gas, Mining, and Logistics are seeing more and more prevalence when it comes to their security status.
Malicious actors have realised how many of these organisations use out-dated operating systems. The lack of visibility into sensors such as pressure and flow valves have also become a point of concern.
Comprehensive visibility, active monitoring, and speedy remediation is the only solution when it comes to combating hackers in the Operational Technology space.